As all routers in an area must have the same copy of the database and each route builds its RIB by running SPF algorithm , Intra area routes can only be filtered locally on a router.
Type 1 LSA Filtering can be done in 2 different ways:
- Changing the Administrative Distance of the route
- Using the distribute-list command
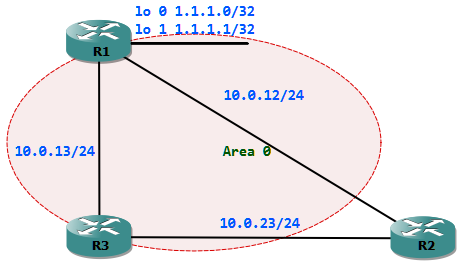
Case 1: The loopback networks of R1 must be filtered from entering the RIB of R2. The 10.0.13.0/24 network must be reachable via R1 and R3.
R2#sh ip route ospf 1.0.0.0/32 is subnetted, 2 subnetsO 1.1.1.1 [110/11] via 10.0.12.1, 00:11:57, FastEthernet0/0O 1.1.1.0 [110/11] via 10.0.12.1, 00:00:04, FastEthernet0/0 10.0.0.0/24 is subnetted, 3 subnetsO 10.0.13.0 [110/20] via 10.0.23.3, 00:08:36, FastEthernet0/1 [110/20] via 10.0.12.1, 00:09:35, FastEthernet0/0Method 1: Filtering by manipulating AD.
First we have to create a standard access-list which permits the loopback networks
R2(config)#ip access-list standard PERMIT_R1_LOOPBACKSR2(config-std-nacl)#permit 1.1.1.0 0.0.0.1R2(config-std-nacl)#router ospf 1R2(config-router)#distance 255 11.11.11.11 0.0.0.0 PERMIT_R1_LOOPBACKSR2(config-router)#do sh ip route ospf 10.0.0.0/24 is subnetted, 3 subnetsO 10.0.13.0 [110/20] via 10.0.23.3, 00:00:09, FastEthernet0/1 [110/20] via 10.0.12.1, 00:00:09, FastEthernet0/0- Access-list
- Prefix-list
- Route-map
First we will use an access-list to filter. For this we have to create an ACL which denies the loopback networks. The second statement in the ACL must permit the rest networks
R2(config)#ip access-list standard DENY_R1_LOOPBACKS
R2(config-std-nacl)#deny 1.1.1.0 0.0.0.1
R2(config-std-nacl)#permit any
Then we could apply the ACL using the distribute-list command under the OSPF process.
R2(config)#router ospf 1
R2(config-router)#distribute-list DENY_R1_LOOPBACKS in
R2(config-router)#do sh ip route ospf
10.0.0.0/24 is subnetted, 3 subnets
O 10.0.13.0 [110/20] via 10.0.23.3, 00:00:05, FastEthernet0/1
[110/20] via 10.0.12.1, 00:00:05, FastEthernet0/0
Now we will use a prefix-list for applying the same filter. A prefix-list must be created which denies the loopback networks and permit the rest.
R2(config)#ip prefix-list DENY_R1_LOOPBACKS deny 1.1.1.0/31 le 32
R2(config)#ip prefix-list DENY_R1_LOOPBACKS permit 0.0.0.0/0 le 32
Then we could apply the prefix-list using the distribute-list command under the OSPF process.
R2(config)#router ospf 1
R2(config-router)#distribute-list prefix DENY_R1_LOOPBACKS in
R2(config-router)#do sh ip route ospf
10.0.0.0/24 is subnetted, 3 subnets
O 10.0.13.0 [110/20] via 10.0.23.3, 00:00:04, FastEthernet0/1
[110/20] via 10.0.12.1, 00:00:04, FastEthernet0/0
The last method and the most granular method to filter is by using a route-map. For this we have to first create a route-map which denies the loopback networks and premiting the rest.
R2(config)#route-map DENY_R1_LOOPBACKS deny
R2(config-route-map)#match ip address PERMIT_R1_LOOPBACKS
R2(config-route-map)#route-map DENY_R1_LOOPBACKS permit 100
The initial sequence number 10 denies the networks described in the access-list PERMIT_R1_LOOPBACKS. The sequence number 100 permits the rest networks, we must use this because of the explicit deny at the end of a route-map.
R2(config-route-map)#do sh route-map
route-map DENY_R1_LOOPBACKS, deny, sequence 10
Match clauses:
ip address (access-lists): PERMIT_R1_LOOPBACKS
Set clauses:
Policy routing matches: 0 packets, 0 bytes
route-map DENY_R1_LOOPBACKS, permit, sequence 100
Match clauses:
Set clauses:
Policy routing matches: 0 packets, 0 bytes
Then we could apply the route-map using the distribute-list command under the OSPF process.
R2(config)#router ospf 1
R2(config-router)#distribute-list route-map DENY_R1_LOOPBACKS in
R2(config-router)#do sh ip route ospf
10.0.0.0/24 is subnetted, 3 subnets
O 10.0.13.0 [110/20] via 10.0.23.3, 00:00:03, FastEthernet0/1
[110/20] via 10.0.12.1, 00:00:03, FastEthernet0/0
Filtering with distribute-list command is always applied in inbound direction. This is because we can only filter the Type 1 LSAs from entering the RIB of the local router.
Case 2: The loopback networks of R1 must be filtered from entering the RIB of R2. The 10.0.13.0/24 network must be reachable only via R3.
The network 10.0.13.0/24 is announced by R1 and R3, Thus R2 has R1 and R3 as next hops to reach it. We cannot use the distance command, because it is not possible to specify the next hop.
Note: We cannot use the route source to filter, because the DR of the segment will be the route source and it could change. To overcome the DR issue we could also change the network type appropriately.
The distribute-list command could be applied in this case using a route-map which could match the next hop.
First we create an access-list which permits the next-hop of 10.0.12.1, network 10.0.13.0 and loopbacks from R1
R2(config)#ip access-list standard NEXTHOPR2(config-std-nacl)#permit host 10.0.12.1R2(config)#ip access-list standard NET_13R2(config-std-nacl)#permit host 10.0.13.0 R2(config)#ip access-list standard R1_LOOPBACKSR2(config-std-nacl)#permit 1.1.1.0 0.0.0.1These access-lists are referred in a route-map which denies them. We must again permit the rest networks at the end of the route-map with a no matching statement.
R2(config)#route-map FILTER denyR2(config-route-map)#match ip next-hop NEXTHOPR2(config-route-map)#match ip address NET_13R2(config-route-map)#route-map FILTER deny 20R2(config-route-map)#match ip address R1_LOOPBACKSR2(config-route-map)#route-map FILTER permit 100 Finally we apply this to the ospf process with a distribute-list again in the inbound direction.
R2(config)#router ospf 1R2(config-router)#distribute-list route-map FILTER inR2(config-router)#do sh ip route ospf 10.0.0.0/24 is subnetted, 3 subnetsO 10.0.13.0 [110/20] via 10.0.23.3, 00:00:03, FastEthernet0/1